How To: Inspect SSH Key Fingerprints
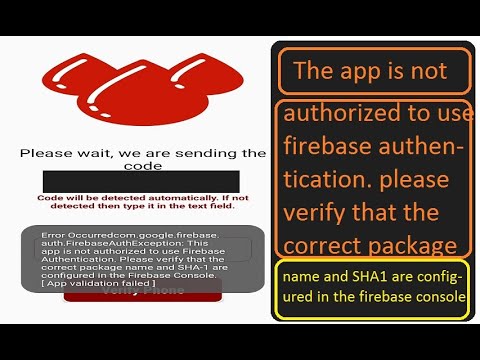
To generate an API key you require, SHA1 fingerprint of your keystore. Keystore is basically a place where the private keys for your app are kept. In simple words its a certificate generated by user or a program, used for signing an Android app. To get the fingerprint(SHA1 ) just follow the below instructions: Step 1: Go to - C:Program FilesJavajdk1.7.025bin Step 2: Inside the bin folder there is a.exe file which is named as 'jarsigner.exe'. Double click on the.exe file and run it. We use the keytool to generate the SHA1 fingerprint. Navigate to the bin directory in your default JDK installation location, which is what you've configured in the JAVAHOME variable, for example, C: Program Files Java jdk 1.7.071. Then select, File Open command prompt. Now, the command prompt window will open. Make sure that you have the SHA fingerprint of your signing certificate. In your Project settings, go to the Your apps card. Select the Firebase Android app to which you want to add a SHA fingerprint. Click Add fingerprint. Enter or paste the SHA fingerprint, then click Save.
As you can imagine, SSH keypairs – combinations of private and public keys – are vital elements of your digital identity as a sysadmin or a developer. And since they can be used for accessing source code repositories and for deploying changes to production environments, you usually have more than one SSH key. That’s why it’s important to know how to inspect SSH key fingerprints.
The SHA1 fingerprint hash displayed by web browsers usually (but not always) use UPPERCASE “hexadecimal” formatting, and usually (but not always) separate each pair of characters with a colon. That's why this web page chose that most common display format. If your browser uses lowercase and/or uses spaces instead of colons, those are just.
SSH Key Fingerprints
Key fingerprints are special checksums generated based on the public SSH key. Run against the same key, ssh-keygen command will always generate the same fingerprint.
Because of this property, you can use SSH key fingerprints for three things:
- Identify SSH key – fingerprint will stay the same even if you rename the file
- Confirm integrity of the SSH key – if you get the same fingerprint from your private SSH key, you can be sure it’s still valid and intact
- Validate identity of the SSH key – same fingerprint means you’re dealing with the same key (that you or your solution trusted for specific functionality)
How to Check SSH Fingerprint of a Key
ssh-keygen command takes the identity (SSH key) filename and calculates the fingerprint.
You can start by changing directory into .ssh and checking if you have any SSH keys there already. If not, you should generate a new SSH key.
Let’s run ssh-keygen to confirm the fingerprint of the id_rsa keypair:
Check Fingerprint of the Private SSH Key
By default this command looks for the public key portion (id_rsa.pub file), so it’s not a very good test of integrity or identity of the private key. There is a very real possibility that you have one private key and a separate public key, that are not related to each other.
That’s why for checking the private key you must take it a step further and copy private key (id_rsa) into some other directory where you can use ssh-keygen again:
this time, because there’s no public key file found nearby, the ssh-keygen command will have to open private key. And if it’s passphrase protected (as it always should be), you’ll be asked for the SSH key passphrase:

Old-school SSH fingerprints
If you’ve been using Linux/Unix for more than a couple of years, you probably noticed that ssh-keygen now shows you a different looking fingerprints: they used to be these semicolon-delimited sequences like this:
… instead they now are shown as this:

The reason for this is that by default fingerprints are shown as SHA256 sequences, while in the past they were MD5.
In order to show the SSH fingerprint in MD5 format, just specify this in the command line:
See also
Isn't SHA-1 deprecated?
Today, many applications still rely on SHA-1, even though theoretical attacks have been known since 2005, and SHA-1 was officially deprecated by NIST in 2011. We hope our practical attack on SHA-1 will increase awareness and convince the industry to quickly move to safer alteratives, such as SHA-256.
How can I protect myself?
You can use our file tester above to check your files. If you use Chrome, you will be automatically protected from insecure TLS/SSL certificates, and Firefoxhas this feature planned for early 2017 has quickly reacted to this announcement, and deprecated SHA-1 as of February 24th, 2017.
Files sent via Gmail or saved in Google Drive are already automatically tested against this attack.
What types of systems are affected?
Any application that relies on SHA-1 for digital signatures, file integrity, or file identification is potentially vulnerable. These include:
- Digital Certificate signatures
- Email PGP/GPG signatures
- Software vendor signatures
- Software updates
- ISO checksums
- Backup systems
- Deduplication systems
- GIT
- ...
Are TLS/SSL certificates at risk?
Any Certification Authority abiding by the CA/Browser Forum regulations is not allowed to issue SHA-1 certificates anymore. Furthermore, it is required that certificate authorities insert at least 64 bits of randomness inside the serial number field. If properly implemented this helps preventing a practical exploitation.
Will my browser show me a warning?
Starting from version 56, released in January 2017, Chrome will consider any website protected with a SHA-1 certificate as insecure. Firefoxhas this feature planned for early 2017 has deprecated SHA-1 as of February 24th, 2017.
Is GIT affected?
GIT strongly relies on SHA-1 for the identification and integrity checking of all file objects and commits. It is essentially possible to create two GIT repositories with the same head commit hash and different contents, say a benign source code and a backdoored one. An attacker could potentially selectively serve either repository to targeted users. This will require attackers to compute their own collision.
Is SVN affected?
SVN has been patched against the attack: versions 1.9.6 and up are immune to it, as well as the 1.8.18 maintenance release.
Previous version are '>affected by the attack. Subversion servers use SHA-1 for deduplication and repositories become corrupted when two colliding files are committed to the repository. This has been discovered in WebKit's Subversion repository and independently confirmed by us. We noticed that in some cases, due to the corruption, further commits are blocked.
How do I patch/upgrade my system?
Consider using safer alternatives, such as SHA-256, or SHA-3.
How do I detect this attack?
You can use the online tool above to submit files and have them checked for a cryptanalytic collision attack on SHA-1. The code behind this was developed by Marc Stevens (CWI) and Dan Shumow (Microsoft) and is publicly available on GitHub.
It is based on the concept of counter-cryptanalysis and it is able to detect known and unknown SHA-1 cryptanalytic collision attacks given just a single file from a colliding file pair.
How widespread is this?
As far as we know our example collision is the first ever created.
Has this been abused in the wild?
Not as far as we know.
Is Hardened SHA-1 vulnerable?
No, SHA-1 hardened with counter-cryptanalysis (see ‘how do I detect the attack’) will detect cryptanalytic collision attacks. In that case it adjusts the SHA-1 computation to result in a safe hash. This means that it will compute the regular SHA-1 hash for files without a collision attack, but produce a special hash for files with a collision attack, where both files will have a different unpredictable hash.
Who is capable of mounting this attack?
This attack required over 9,223,372,036,854,775,808 SHA1 computations. This took the equivalent processing power as 6,500 years of single-CPU computations and 110 years of single-GPU computations.
How does this attack compare to the brute force one?

Sha1 Generator Windows
The SHAttered attack is 100,000 faster than the brute force attack that relies on the birthday paradox. The brute force attack would require 12,000,000 GPU years to complete, and it is therefore impractical.
How did you leverage the PDF format for this attack?
A picture is worth a thousand words, so here it is.Who is the team behind this research?
Sha1 Generator Online
This result is the product of a long term collaboration between the Cryptology Group at Centrum Wiskunde & Informatica (CWI) - the national research institute for mathematics and computer science in the Netherlands - and the Google Research Security, Privacy and Anti-abuse Group. Two years ago Marc Stevens and Elie Bursztein, who leads the Google's anti-abuse research team, began collaborating on making Marc's cryptanalytic attacks against SHA-1 practical by leveraging Google expertise and infrastructure. Since then many CWI researchers and Googlers have helped make this project possible, including Pierre Karpman who worked on the cryptanalysis and prototype GPU implementation, and from Google Ange Albertini who developed the PDF attack, Yarik Markov who took care of the distributed GPU code, Alex Petit-Bianco implemented the collision detector to protect Google users, Luca Invernizzi who created the online file checker, and Clement Blaisse who oversaw the reliability of the computations.